Secure Identity (Authentication)
NanoLog uses a secure mechanism to authenticate users across domains, allowing you to uniquely identify your active logged-in users inside the widget without relying on third-party cookies or cross-site tracking. This is crucial for segmentation, identifying who is voting, and providing context for feedback.
Why use Secure Identity?
When a user visits your platform, the NanoLog widget needs to know who they are. Because of strict modern browser privacy rules, cookies cannot be reliably shared across domains. Secure Identity solves this by passing a cryptographic JSON Web Token (JWT) or HMAC signature securely from your backend directly into the NanoLog initialization script.
This guarantees that:
- Malicious actors cannot spoof a user's identity to leave fake feedback.
- Voting is securely tied to genuine user accounts.
- You can effectively segment posts (e.g., only show "Pro Features" updates to Pro users).
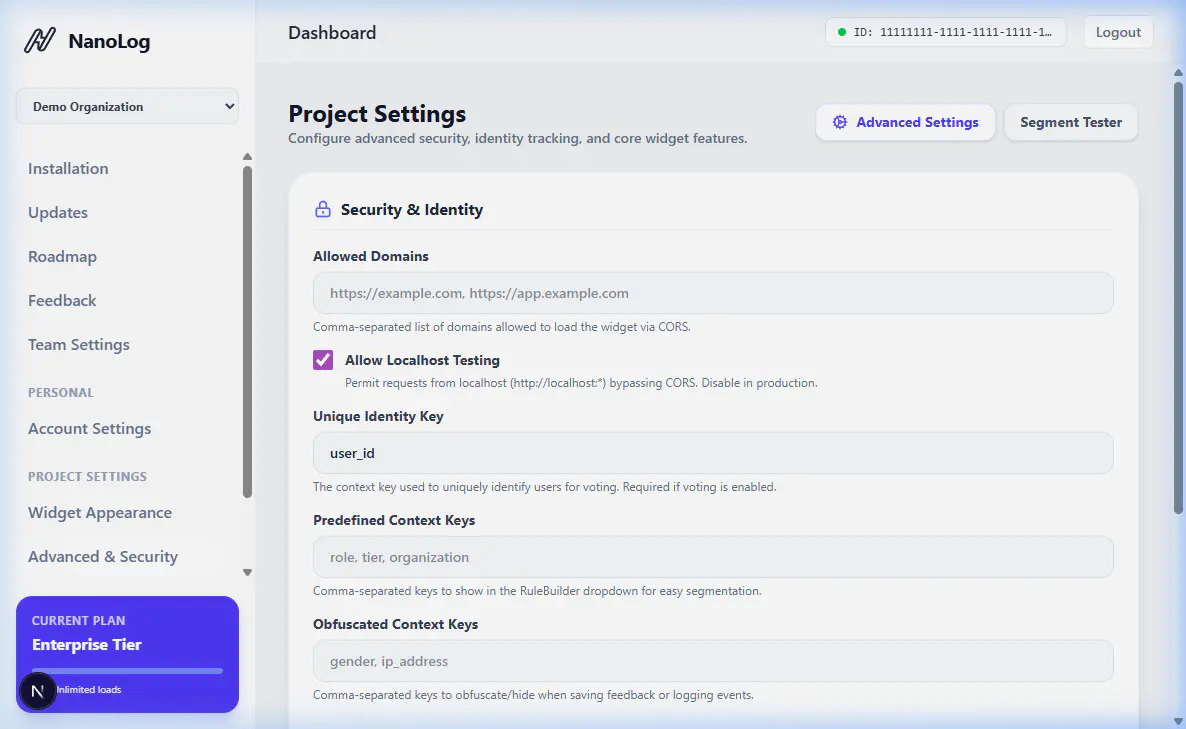
Setting up Secure Identity
1. Generating the Token on your Backend
You will need to generate a secure token on your server when rendering the widget snippet for an authenticated user. You must use the SECRET_KEY provided in your NanoLog project settings.
Here is an example in Node.js of how you might generate this token:
const crypto = require('crypto');
function generateNanoLogToken(user, secretKey) {
// Define the user payload
const payload = {
id: user.id,
email: user.email,
name: user.name,
plan: user.plan
};
// Create HMAC signature
const data = JSON.stringify(payload);
const hmac = crypto.createHmac('sha256', secretKey);
hmac.update(data);
const signature = hmac.digest('hex');
return { payload: data, signature: signature };
}
2. Passing the Token to the Widget
Once your backend has generated the signature and the payload, you must inject them into the NanoLog Javascript Snippet when the page loads for the client.
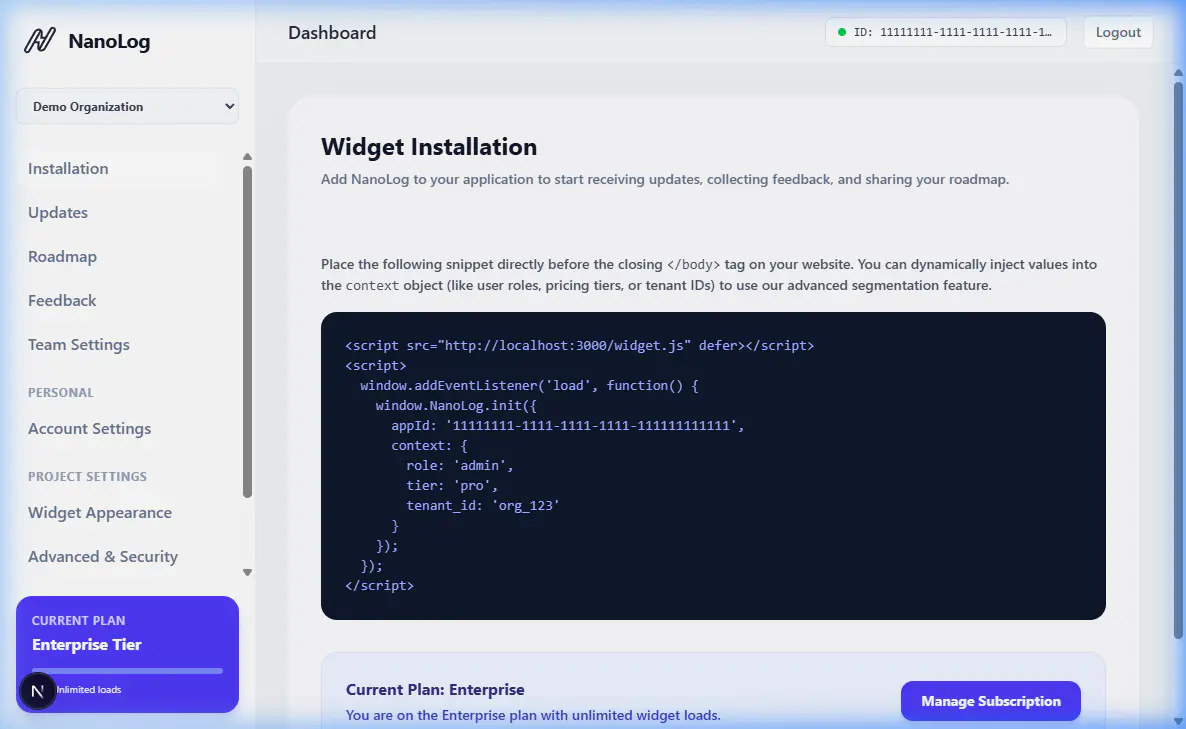
Update your widget initialization code to include the identity property:
<script src="https://nanolog.com/widget.js" data-app-id="YOUR_APP_ID"></script>
<script>
window.NanoLog.init({
identity: {
payload: '{"id":"user_123","email":"test@test.com","plan":"pro"}',
signature: 'a8b7c6d5e4f3...' // The HMAC signature generated above
}
});
</script>
Once correctly configured, NanoLog will automatically verify the signature and attribute all subsequent interactions (votes, tracking, feedback) to that verified user.